At ValidExamDumps, we consistently monitor updates to the VMware 3V0-41.22 exam questions by VMware. Whenever our team identifies changes in the exam questions,exam objectives, exam focus areas or in exam requirements, We immediately update our exam questions for both PDF and online practice exams. This commitment ensures our customers always have access to the most current and accurate questions. By preparing with these actual questions, our customers can successfully pass the VMware Advanced Deploy VMware NSX-T Data Center 3.x exam on their first attempt without needing additional materials or study guides.
Other certification materials providers often include outdated or removed questions by VMware in their VMware 3V0-41.22 exam. These outdated questions lead to customers failing their VMware Advanced Deploy VMware NSX-T Data Center 3.x exam. In contrast, we ensure our questions bank includes only precise and up-to-date questions, guaranteeing their presence in your actual exam. Our main priority is your success in the VMware 3V0-41.22 exam, not profiting from selling obsolete exam questions in PDF or Online Practice Test.
SIMULATION
Task 10
You have been notified by the Web Team that they cannot get to any northbound networks from their Tampa web servers that are deployed on an NSX-T
network segment. The Tampa web VM's however can access each other.
You need to:
* Troubleshoot to find out why the Tampa web servers cannot communicate to any northbound networks and resolve the issue.
Complete the requested task. TO verify your work. ping the Control Center @ 192.168.110.10
Notes: Passwords are contained in the user_readme.txt. This task is dependent on Task 4. Some exam candidates may have already completed this task if they had done more than the minimum required in Task 4. This task should take approximately 15 minutes to complete.
To troubleshoot why the Tampa web servers cannot communicate to any northbound networks, you need to follow these steps:
Log in to the NSX Manager UI with admin credentials. The default URL is https://<nsx-manager-ip-address>.
Navigate to Networking > Tier-0 Gateway and select the tier-0 gateway that connects the NSX-T network segment to the northbound networks. For example, select T0-GW-01.
Click Interfaces > Set and verify the configuration details of the interfaces. Check for any discrepancies or errors in the parameters such as IP address, subnet mask, MTU, etc.
If you find any configuration errors, click Edit and modify the parameters accordingly. Click Save to apply the changes.
If you do not find any configuration errors, check the connectivity and firewall rules between the tier-0 gateway and the northbound networks. You can use ping or traceroute commands from the NSX Edge CLI or the vSphere Web Client to test the connectivity. You can also use show service router command to check the status of the routing service on the NSX Edge.
If you find any connectivity or firewall issues, resolve them by adjusting the network settings or firewall rules on the NSX Edge or the northbound devices.
SIMULATION
Task 4
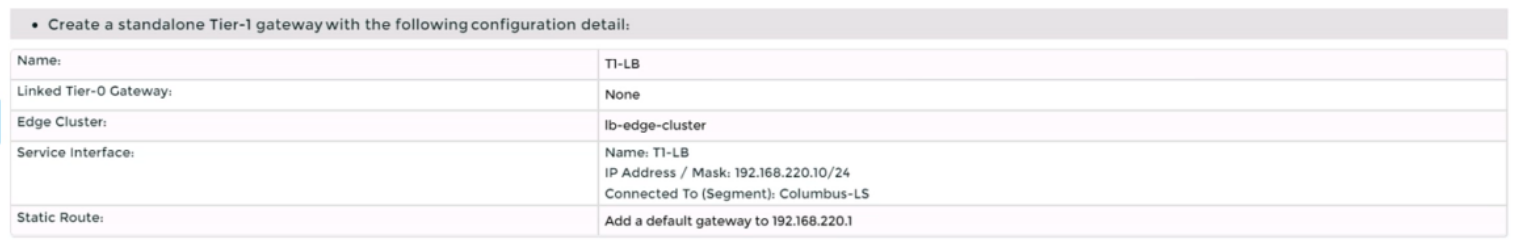
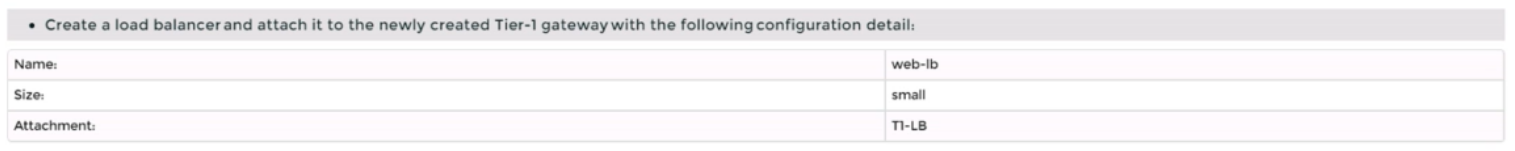
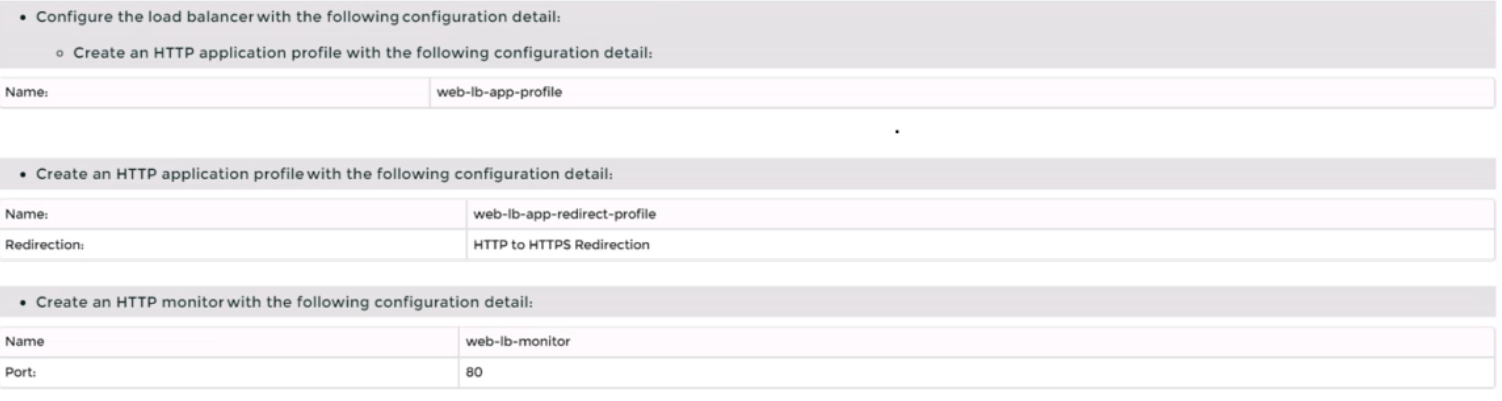
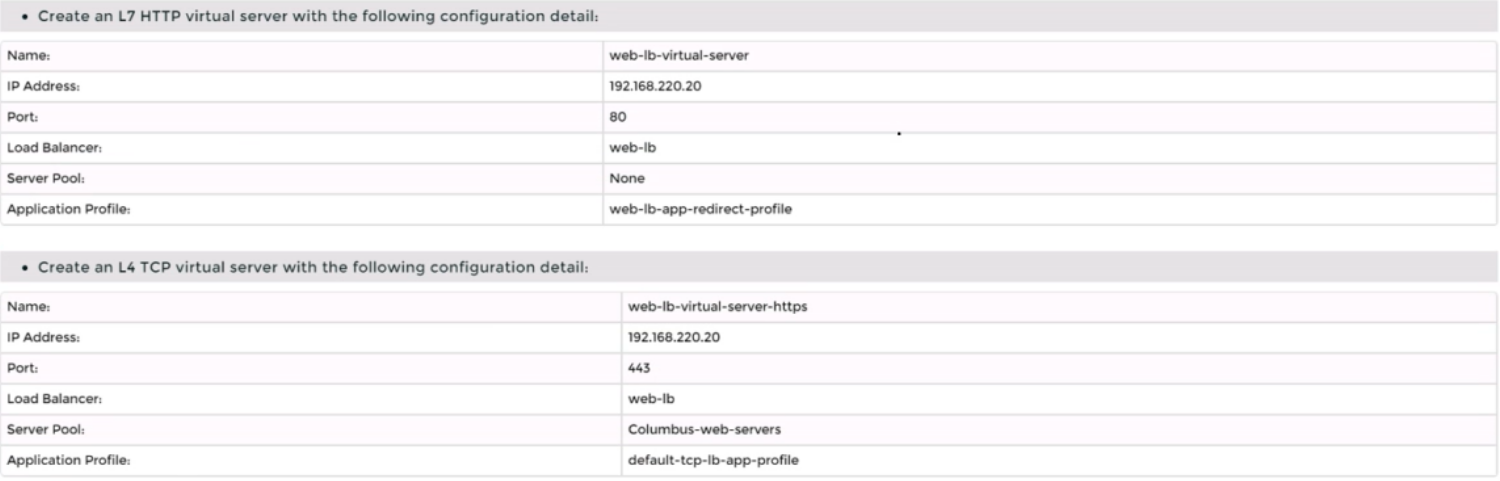
You are tasked with creating a logical load balancer for several web servers that were recently deployed.
You need to:
Complete the requested task.
Notes:
Passwords are contained in the user_readme.txt. Do not wait for configuration changes to be applied in this task as processing may take some time to complete. This task should take up to 35 minutes to complete and is required for subsequent tasks.
To create a logical load balancer for several web servers, you need to follow these steps:
Log in to the NSX Manager UI with admin credentials. The default URL is https://<nsx-manager-ip-address>.
Navigate to Networking > Load Balancing > Load Balancers and click Add Load Balancer.
Enter a name and an optional description for the load balancer. Select the tier-1 gateway where you want to attach the load balancer from the drop-down menu or create a new one by clicking New Tier-1 Gateway. Click Save.
Navigate to Networking > Load Balancing > Application Profiles and click Add Application Profile.
Enter a name and an optional description for the application profile. Select HTTP as the application type from the drop-down menu. Optionally, you can configure advanced settings such as persistence, X-Forwarded-For, SSL offloading, etc., for the application profile. Click Save.
Navigate to Networking > Load Balancing > Monitors and click Add Monitor.
Enter a name and an optional description for the monitor. Select HTTP as the protocol from the drop-down menu. Optionally, you can configure advanced settings such as interval, timeout, fall count, rise count, etc., for the monitor. Click Save.
Navigate to Networking > Load Balancing > Server Pools and click Add Server Pool.
Enter a name and an optional description for the server pool. Select an existing application profile from the drop-down menu or create a new one by clicking New Application Profile. Select an existing monitor from the drop-down menu or create a new one by clicking New Monitor. Optionally, you can configure advanced settings such as algorithm, SNAT translation mode, TCP multiplexing, etc., for the server pool. Click Save.
Click Members > Set > Add Member and enter the IP address and port number of each web server that you want to add to the server pool. For example, enter 192.168.10.10:80 and 192.168.10.11:80 for two web servers listening on port 80. Click Save and then Close.
Navigate to Networking > Load Balancing > Virtual Servers and click Add Virtual Server.
Enter a name and an optional description for the virtual server. Enter the IP address and port number of the virtual server that will receive the client requests, such as 10.10.10.100:80. Select HTTP as the service profile from the drop-down menu or create a new one by clicking New Service Profile. Select an existing server pool from the drop-down menu or create a new one by clicking New Server Pool. Optionally, you can configure advanced settings such as access log, connection limit, rate limit, etc., for the virtual server. Click Save.
SIMULATION
Task 15
You have been asked to enable logging so that the global operations team can view inv Realize Log Insight that their Service Level Agreements are being met for all network traffic that is going in and out of the NSX environment. This NSX environment is an Active / Active two Data Center design utilizing N-VDS with BCP. You need to ensure successful logging for the production NSX-T environment.
You need to:
Verify via putty with SSH that the administrator can connect to all NSX-Transport Nodes. You will use the credentials identified in Putty (admin).
Verify that there is no current active logging enabled by reviewing that directory is empty -/var/log/syslog-
Enable NSX Manager Cluster logging
Select multiple configuration choices that could be appropriate success criteria
Enable NSX Edge Node logging
Validate logs are generated on each selected appliance by reviewing the "/var/log/syslog''
Complete the requested task.
Notes: Passwords are contained in the user _ readme.txt. complete.
These task steps are dependent on one another. This task should take approximately 10 minutes to complete.
To enable logging for the production NSX-T environment, you need to follow these steps:
Verify via putty with SSH that the administrator can connect to all NSX-Transport Nodes. You can use the credentials identified in Putty (admin) to log in to each transport node. For example, you can use the following command to connect to the sfo01w01en01 edge transport node: ssh admin@sfo01w01en01. You should see a welcome message and a prompt to enter commands.
Verify that there is no current active logging enabled by reviewing that directory is empty -/var/log/syslog-. You can use the ls command to list the files in the /var/log/syslog directory. For example, you can use the following command to check the sfo01w01en01 edge transport node: ls /var/log/syslog. You should see an empty output if there is no active logging enabled.
Navigate to System > Fabric > Profiles > Node Profiles then select All NSX Nodes then under Syslog Servers click +ADD
Enter the IP or FQDN of the syslog server, the Port and Protocol and the desired Log Level then click ADD
Select multiple configuration choices that could be appropriate success criteri
a. You can use the search_web('NSX-T logging success criteria') tool to find some information on how to verify and troubleshoot logging for NSX-T. Some of the possible success criteria are:
The syslog server receives log messages from all NSX nodes
The log messages contain relevant information such as timestamp, hostname, facility, severity, message ID, and message content
The log messages are formatted and filtered according to the configured settings
The log messages are encrypted and authenticated if using secure protocols such as TLS or LI-TLS
Run the following command to configure a log server and the types of messages to send to the log server. Multiple facilities or message IDs can be specified as a comma delimited list, without spaces.
set logging-server <hostname-or-ip-address [:port]> proto
Validate logs are generated on each selected appliance by reviewing the '/var/log/syslog''. You can use the cat or tail commands to view the contents of the /var/log/syslog file on each appliance. For example, you can use the following command to view the last 10 lines of the sfo01w01en01 edge transport node: tail -n 10 /var/log/syslog. You should see log messages similar to this:
2023-04-06T12:34:56+00:00 sfo01w01en01 user.info nsx-edge[1234]: 2023-04-06T12:34:56Z nsx-edge[1234]: INFO: [nsx@6876 comp='nsx-edge' subcomp='nsx-edge' level='INFO' security='False'] Message from nsx-edge
You have successfully enabled logging for the production NSX-T environment.
SIMULATION
Task 8
You are tasked With troubleshooting the NSX IPSec VPN service Which has been reported down. Verify the current NSX configuration is deployed and resolve any issues.
You need to:
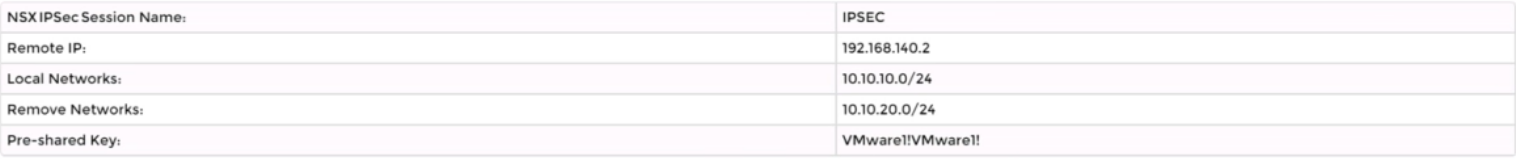
* Verify the present configuration as provided below:
Complete the requested task.
Notes: Passwords are contained in the user_readme.txt. This task is not dependent on another. This task Should take approximately 15 minutes to complete.
To troubleshoot the NSX IPSec VPN service that has been reported down, you need to follow these steps:
Log in to the NSX Manager UI with admin credentials. The default URL is https://<nsx-manager-ip-address>.
Navigate to Networking > VPN > IPSec VPN and select the IPSec VPN session that is down. You can identify the session by its name, local endpoint, remote endpoint, and status.
Click Show IPSec Statistics and view the details of the IPSec VPN session failure. You can see the error message, the tunnel state, the IKE and ESP status, and the statistics of the traffic sent and received.
Compare the configuration details of the IPSec VPN session with the expected configuration as provided below. Check for any discrepancies or errors in the parameters such as local and remote endpoints, local and remote networks, IKE and ESP profiles, etc.
If you find any configuration errors, click Actions > Edit and modify the parameters accordingly. Click Save to apply the changes.
If you do not find any configuration errors, check the connectivity and firewall rules between the local and remote endpoints. You can use ping or traceroute commands from the NSX Edge CLI to test the connectivity. You can also use show service ipsec command to check the status of IPSec VPN service on the NSX Edge.
If you find any connectivity or firewall issues, resolve them by adjusting the network settings or firewall rules on the NSX Edge or the third-party device.
SIMULATION
Task 2
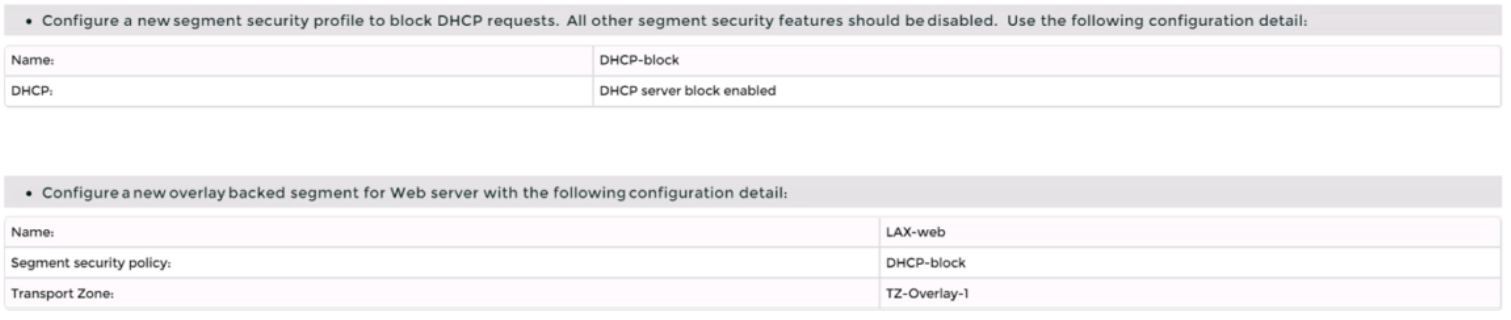
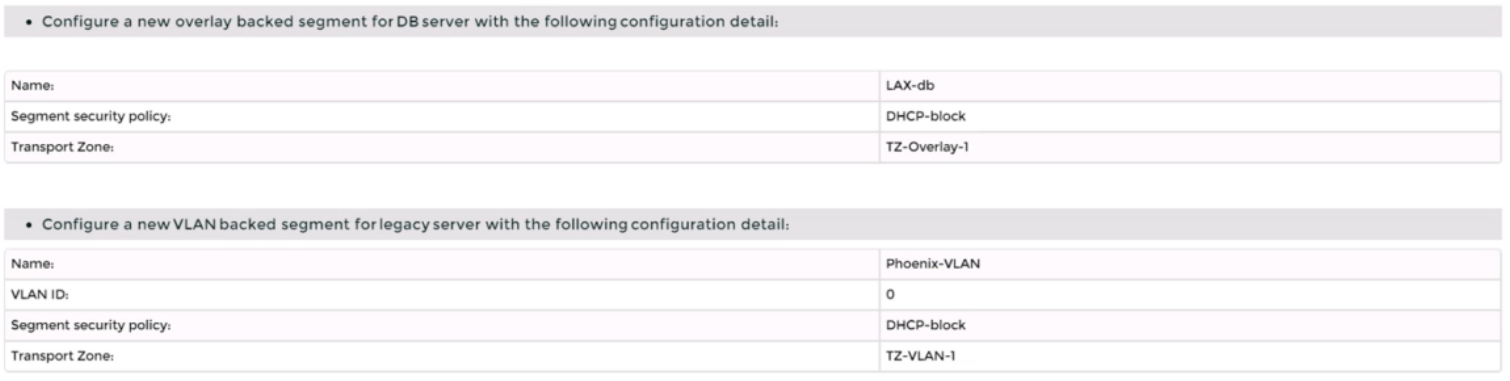
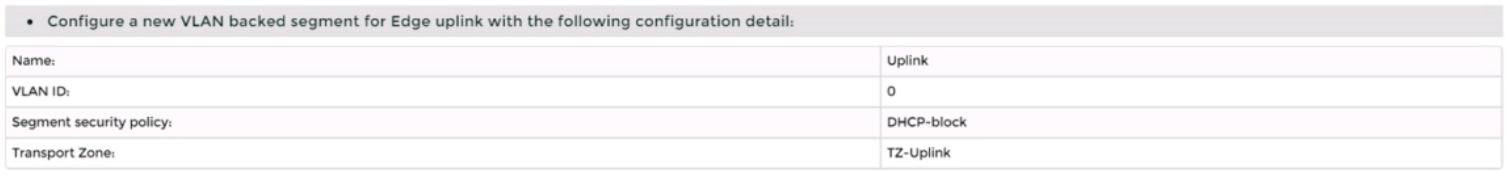
You are asked to deploy three Layer 2 overlay-backed segments to support a new 3-tier app and one Layer 2 VLAN-backed segment for support of a legacy application. The logical segments must block Server DHCP requests. Ensure three new overlay-backed segments and one new VLAN-backed logical segment are deployed to the RegionA01-COPMOI compute cluster. All configuration should be done utilizing the NSX UI.
You need to:
Complete the requested task.
Notes: Passwords are contained in the user_readme.txt. Task 2 is dependent on the completion of Task 1. Other tasks are dependent on completion of this task. You may want to move to the next tasks while waiting for configuration changes to be applied. This task should take approximately 10 minutes to complete.
To deploy three layer 2 overlay-backed segments and one layer 2 VLAN-backed segment, you need to follow these steps:
Log in to the NSX Manager UI with admin credentials. The default URL is https://<nsx-manager-ip-address>.
Navigate to Networking > Segments and click Add Segment.
Enter a name for the segment, such as Web-01.
Select Tier-1 as the connectivity option and choose an existing tier-1 gateway from the drop-down menu or create a new one by clicking New Tier-1 Gateway.
Enter the gateway IP address of the subnet in a CIDR format, such as 192.168.10.1/24.
Select an overlay transport zone from the drop-down menu, such as Overlay-TZ.
Optionally, you can configure advanced settings such as DHCP, Metadata Proxy, MAC Discovery, or QoS for the segment by clicking Set Advanced Configs.
Click Save to create the segment.
Repeat steps 2 to 8 for the other two overlay-backed segments, such as App-01 and DB-01, with different subnet addresses, such as 192.168.20.1/24 and 192.168.30.1/24.
To create a VLAN-backed segment, click Add Segment again and enter a name for the segment, such as Legacy-01.
Select Tier-0 as the connectivity option and choose an existing tier-0 gateway from the drop-down menu or create a new one by clicking New Tier-0 Gateway.
Enter the gateway IP address of the subnet in a CIDR format, such as 10.10.10.1/24.
Select a VLAN transport zone from the drop-down menu, such as VLAN-TZ, and enter the VLAN ID for the segment, such as 100.
Optionally, you can configure advanced settings such as DHCP, Metadata Proxy, MAC Discovery, or QoS for the segment by clicking Set Advanced Configs.
Click Save to create the segment.
To apply a segment security profile to block DHCP requests on the segments, navigate to Networking > Segments > Segment Profiles and click Add Segment Profile.
Select Segment Security as the profile type and enter a name and an optional description for the profile.
Toggle the Server Block and Server Block - IPv6 buttons to enable DHCP filtering for both IPv4 and IPv6 traffic on the segments that use this profile.
Click Save to create the profile.
Navigate to Networking > Segments and select the segments that you want to apply the profile to.
Click Actions > Apply Profile and select the segment security profile that you created in step 18.
Click Apply to apply the profile to the selected segments.