At ValidExamDumps, we consistently monitor updates to the Trend Deep-Security-Professional exam questions by Trend. Whenever our team identifies changes in the exam questions,exam objectives, exam focus areas or in exam requirements, We immediately update our exam questions for both PDF and online practice exams. This commitment ensures our customers always have access to the most current and accurate questions. By preparing with these actual questions, our customers can successfully pass the Trend Micro Certified Professional for Deep Security Exam exam on their first attempt without needing additional materials or study guides.
Other certification materials providers often include outdated or removed questions by Trend in their Trend Deep-Security-Professional exam. These outdated questions lead to customers failing their Trend Micro Certified Professional for Deep Security Exam exam. In contrast, we ensure our questions bank includes only precise and up-to-date questions, guaranteeing their presence in your actual exam. Our main priority is your success in the Trend Deep-Security-Professional exam, not profiting from selling obsolete exam questions in PDF or Online Practice Test.
Which of the following statements is true regarding Intrusion Prevention protection?
Which of the following are valid methods for forwarding Event information from Deep Secu-rity? Select all that apply.
You can configure Deep Security Manager to instruct all managed computers to send logs to a SI-EM, Amazon Simple Notification Service or SNMP computers.
Explication: Study Guide - page (322)
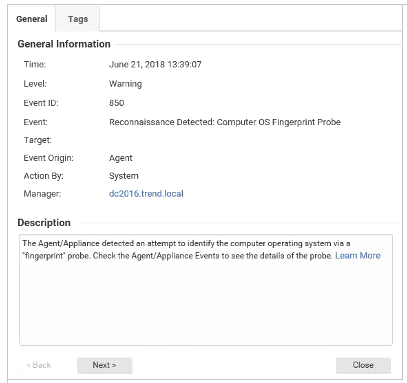
Based on the details of event displayed in the exhibit, which of the following statements is false?
A collection of servers protected by Deep Security do not have Internet access. How can Smart Scan be used on these computers.
Agent-airgapped
Which of the following statements correctly describes Smart Folders?
Smart Folders are used to group your computers dynamically. The computers displayed in a Smart Folder are determined by a set of custom rules, that act as a saved search which is executed each time you click on the folder to display its contents. This allows administrators to easily filter and group computers by these defined properties.
Explication: Study Guide - page (127)