At ValidExamDumps, we consistently monitor updates to the Linux Foundation CKS exam questions by Linux Foundation. Whenever our team identifies changes in the exam questions,exam objectives, exam focus areas or in exam requirements, We immediately update our exam questions for both PDF and online practice exams. This commitment ensures our customers always have access to the most current and accurate questions. By preparing with these actual questions, our customers can successfully pass the Linux Foundation Certified Kubernetes Security Specialist exam on their first attempt without needing additional materials or study guides.
Other certification materials providers often include outdated or removed questions by Linux Foundation in their Linux Foundation CKS exam. These outdated questions lead to customers failing their Linux Foundation Certified Kubernetes Security Specialist exam. In contrast, we ensure our questions bank includes only precise and up-to-date questions, guaranteeing their presence in your actual exam. Our main priority is your success in the Linux Foundation CKS exam, not profiting from selling obsolete exam questions in PDF or Online Practice Test.
Analyze and edit the given Dockerfile
FROM ubuntu:latest
RUN apt-get update -y
RUN apt-install nginx -y
COPY entrypoint.sh /
ENTRYPOINT ["/entrypoint.sh"]
USER ROOT
Fixing two instructions present in the file being prominent security best practice issues
Analyze and edit the deployment manifest file
apiVersion: v1
kind: Pod
metadata:
name: security-context-demo-2
spec:
securityContext:
runAsUser: 1000
containers:
- name: sec-ctx-demo-2
image: gcr.io/google-samples/node-hello:1.0
securityContext:
runAsUser: 0
privileged: True
allowPrivilegeEscalation: false
Fixing two fields present in the file being prominent security best practice issues
Don't add or remove configuration settings; only modify the existing configuration settings
Whenever you need an unprivileged user for any of the tasks, use user test-user with the user id 5487
a. Retrieve the content of the existing secret nameddefault-token-xxxxxin the testing namespace.
Store the value of the token in the token.txt
b. Create a new secret named test-db-secret in the DB namespace with the following content:
username:mysql
password:password@123
Create the Pod name test-db-pod of image nginx in the namespace db that can access test-db-secret via a volume at path /etc/mysql-credentials
Create a new NetworkPolicy named deny-all in the namespace testing which denies all traffic of type ingress and egress traffic
Cluster:qa-cluster Master node:masterWorker node:worker1 You can switch the cluster/configuration context using the following command: [desk@cli] $kubectl config use-context qa-cluster Task: Create a NetworkPolicy namedrestricted-policyto restrict access to Podproductrunning in namespacedev. Only allow the following Pods to connect to Pod products-service: 1. Pods in the namespaceqa 2. Pods with labelenvironment: stage, in any namespace
Context
This cluster uses containerd as CRI runtime.
Containerd's default runtime handler is runc. Containerd has been prepared to support an additional runtime handler, runsc (gVisor).
Task
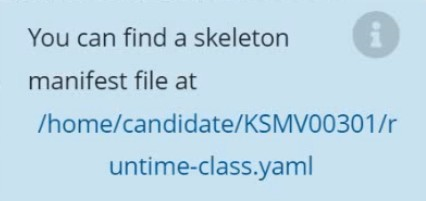
Create a RuntimeClass named sandboxed using the prepared runtime handler named runsc.
Update all Pods in the namespace server to run on gVisor.